Nintex Workflow for SharePoint: optimise your business processes
Discover how Nintex Workflow for SharePoint optimises enterprise workflow automation by using no-code tools for maximum efficiency.
How to create the perfect CV if you are a full stack developer

Find out how to create the perfect CV if you are a full stack developer, with concrete examples, free templates, and all the practical advice you need to stand out from the crowd.
Find out everything you need to know about the job of senior full stack developer

Find out everything you need to know about the job of senior full stack developer: salary, typical assignments, role, responsibilities and career development.
Performance Testing: how to evaluate the performance of your web applications
In the digital age, web application performance is a key success factor for any organisation. Users in the modern world expect a smooth, fast and reliable experience, whether they’re browsing an e-commerce site, using a SaaS application or interacting with online services. According to studies, a response time of more than three seconds can result […]
Job description: data scientist

With the growing importance of data in corporate strategies, the data scientist has become a key player. Their expertise enables them to leverage Big Data to tackle strategic challenges, whether these involve understanding markets, optimising performance or forecasting trends. What is their role, what tasks are entrusted to them and why is this profession so […]
Find out everything there is to know about being a developer

Find out everything there is to know about being a Developer: salary, typical tasks, role, responsibilities and career development.
Test Engineer: everything you need to know about the profession and prospects in German-speaking Switzerland
The digital age demands impeccable software quality, and malfunctions can lead to financial loss or damage to a company’s reputation. This is where the test engineer comes in. In this article, we’ll take a closer look at this profession, to find out about all its facets: skills, missions and essential processes. Overview What is a […]
Cloud security: best practices to adopt

The accelerated pace of the digital transformation poses a growing number challenges for data security in the cloud. What are the current issues and how can you keep your sensitive information protected? Follow our recommendations and discover the best practices for enhanced security. Overview What is Cloud Computing? Cloud computing refers to the provision of […]
Discover everything you need to know about working as a full-stack developer
Discover everything you need to know about working as a full-stack developer: salary, missions, role, responsibilities and career development.
Endpoint Security: securing the devices connected to your network

Find out how to secure every endpoint within your company, with security solutions tailor-made to counter today’s cyberattack threats.
How should you go about getting trained in cybersecurity?
Are you looking to get a qualification in cybersecurity? Whether you’re passionate about IT, looking for a change of career, or already working in the field, this guide will help you choose the best training course in IT security. Discover the professions, recognized training courses, free and online training opportunities, and career prospects in the […]
Two-factor authentication: how can you secure your online access?
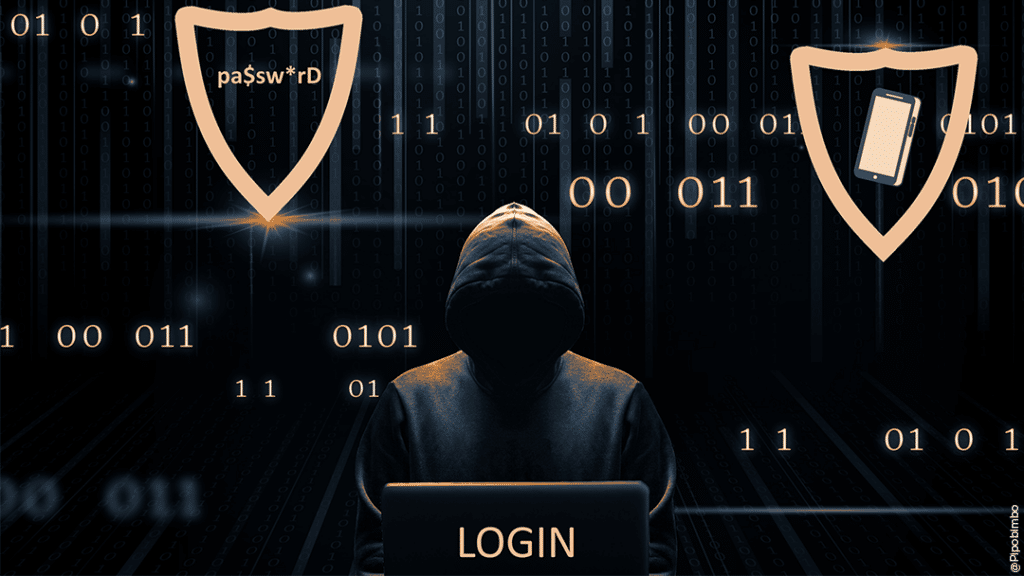
With cyberattacks continuing to increase, protecting online access has become essential for individuals and businesses alike. Data theft, account hacking and other cyberthreats are becoming increasingly common, making traditional passwords less and less secure. Two-factor authentication (2FA) is a security technology that strengthens online account security by adding an extra layer of protection. But how […]