Vous souhaitez renforcer la sécurité de vos projets et avez entendu parler de la sécurité Shift Left ? Cet article vous présentera cette approche, ses avantages, ses outils ainsi que l’accompagnement que Qim info peut vous apporter pour mener à bien sa mise en place.
Sommaire
Shift Left Security : c'est quoi ?
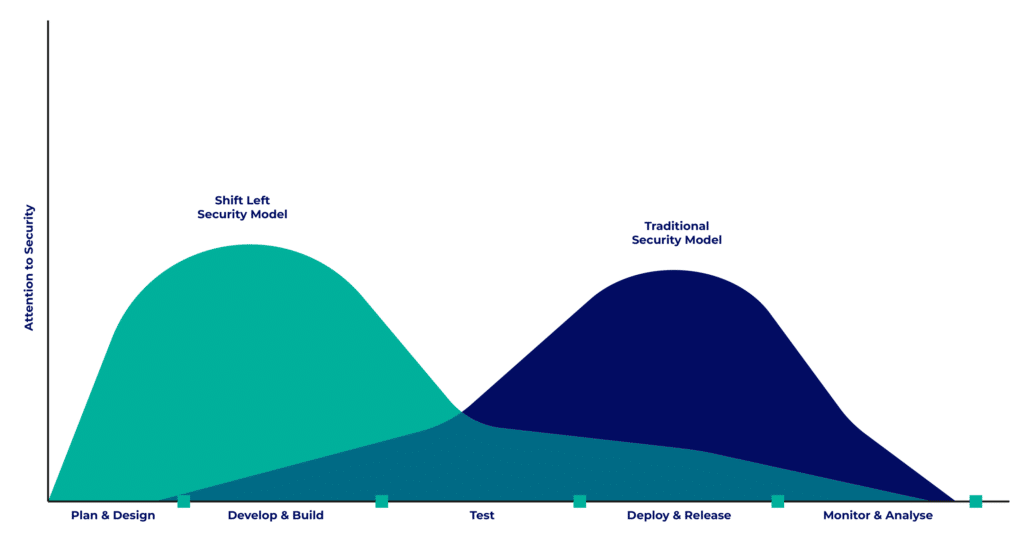
La formule « Shift left » se traduit littéralement par « décaler vers la gauche ». En effet, le cycle de vie de développement logiciel (SDLC) peut être représenté linéairement. Dans ce cas-là, décaler la sécurité à gauche signifie déplacer la sécurité vers le début du cycle.
Dans une majorité des cas, la sécurité est une préoccupation tardive qui s’exprime en fin de phase de test et au moment du déploiement.
L’approche « Shift left security » quant à elle, vise à embarquer les problématiques de sécurité avant même l’écriture du code, dès la phase de planification et de design. Son objectif est donc d’identifier et de résoudre les problèmes de sécurité le plus tôt possible.
Gardez bien ce schéma en tête car d’autres stratégies aux noms similaires existent. Parmi elles, apprenons à bien la différencier de la sécurité Shift Right.
Quelle différence avec le Shift Right ?
L’approche « Shift left » se concentre sur le début du SDLC. Au contraire, la stratégie « Shift right security » se focalise sur la fin du cycle, à partir du déploiement et tout au long de la phase opérationnelle.
Cette approche a pour but d’appliquer une surveillance continue dans l’environnement de production. En effet, de nouvelles menaces et vulnérabilités apparaissent constamment. Adopter l’approche Shift Right permet donc de détecter et corriger ces vulnérabilités le plus rapidement possible durant le fonctionnement, avant qu’elles ne soient exploitées.
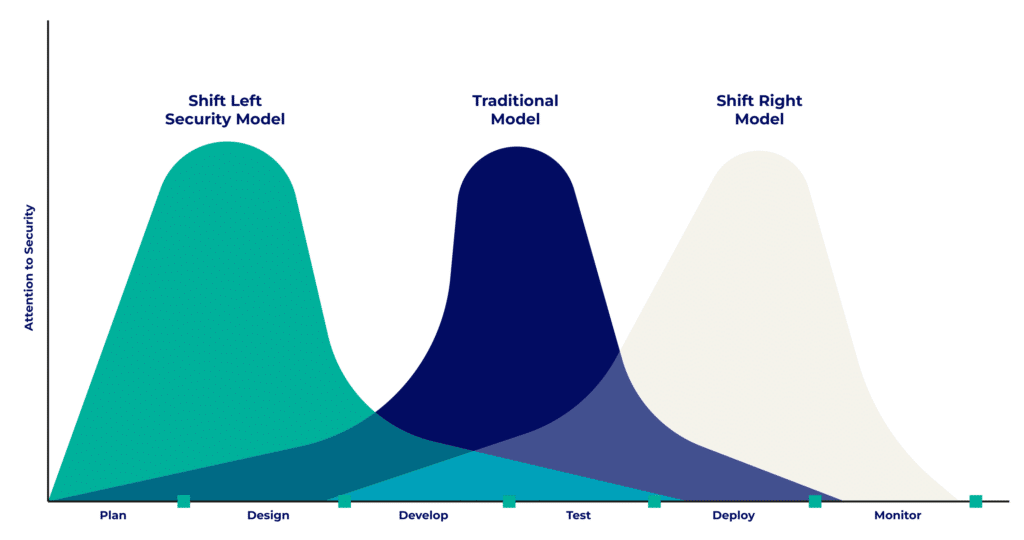
Mettre en place les deux stratégies permet donc une sécurité optimale tout au long du cycle. Si le Shift Right est une approche assez répandue, la stratégie Shift Left est considérée comme plus innovante et apporte de nombreux avantages.
Quels sont les avantages de l'approche Shift Left ?
Détection anticipée des vulnérabilités
L’application de la stratégie Shift Left à la sécurité permet de diminuer le temps de détection des vulnérabilités. Au lieu de toutes les découvrir au moment des tests, elles sont progressivement identifiées tout au long de la phase de développement.
Les équipes peuvent alors aborder l’étape de remédiation plus tôt et ont plus de temps pour appliquer les correctifs
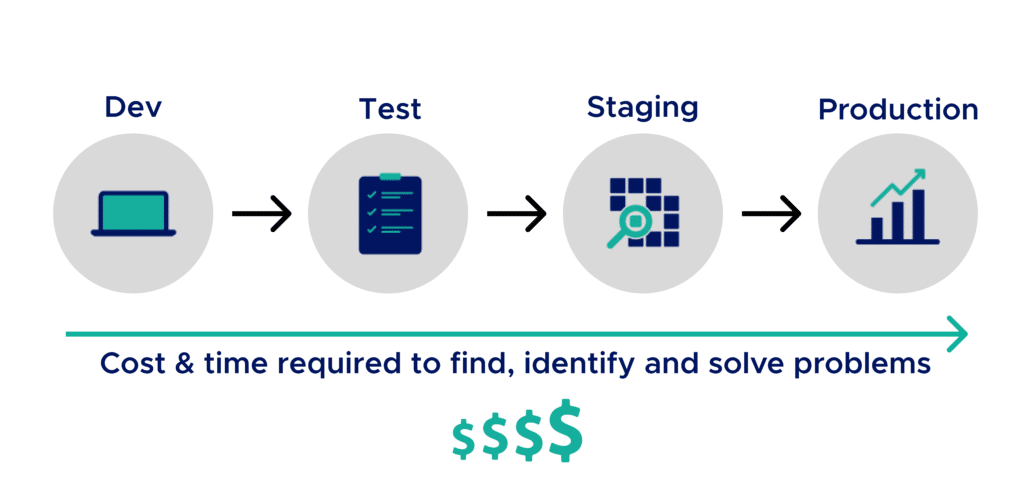
Diminution des coûts de correction
Ce traitement anticipé de la sécurité diminue les coûts de correction.
En effet, la détection précoce permet d’éviter l’accumulation des problèmes de sécurité et ainsi de diminuer la dette technique et les vecteurs d’attaques sur la base de code.
De plus, le ratio entre les équipes de développement, d’exploitation et de sécurité est assez déséquilibré. Appliquer l’approche Shift Left permet de donner une partie des responsabilités de la sécurité aux équipes de développement, plus nombreuses. Cela libère donc du temps aux équipes de sécurité pour effectuer des tâches plus spécifiques et à plus forte valeur ajoutée.
Déplacer la sécurité à gauche est donc un gain de ressources financières et humaines.

Accélération de la mise sur le marché
En plus d’un gain pécuniaire et d’une meilleure utilisation des compétences, l’application de la stratégie Shift Left permet également de diminuer le Time to Market.
Le traitement progressif et anticipé des problèmes de sécurité évite les actions ponctuelles complexes et chronophages, comme les interventions correctives en production de type Hotfix.
La mise sur le marché n’est ainsi plus bloquée par des tests de sécurité nécessitant des retours en arrière. En effet, le temps de résolution des problèmes de sécurité est réparti sur les premières phases du SDLC.
Amélioration de la confiance et de la satisfaction client
Enfin, cette approche renforce la confiance et la satisfaction client. La sécurité est en effet considérée comme un critère de qualité par les développeurs et le produit est « Secure by design ».
Et pour parfaire vos connaissances sur ces thématiques, nous vous conseillons de lire nos articles “Qu’est-ce que le Cloud ?” et “DevOps, c’est quoi ?”
Comment mettre en place le Shift Left Security ?
La mise en place de l’approche Shift Left Security nécessite d’apporter des changements aux étapes de début de cycle.
Dans un premier temps, il est nécessaire de planifier la sécurité. Cela signifie qu’il est important d’analyser et d’identifier les besoins en sécurité afin de les prendre en compte dans le design de la solution. Des tests doivent également être planifiés afin de valider le respect de ces exigences.
La mise en place des tests de sécurité doit également évoluer. Ils doivent être fractionnés en tests plus courts, plus ciblés et intervenir plus tôt dans le cycle.
L’adoption de bonnes pratiques de développement permets de diminuer les sources d’erreurs et ainsi contribuer à la sécurité d’un code source. Celles-ci peuvent par exemple impacter le choix des dépendances ou encore la gestion des secrets.
Enfin, le déplacement de la sécurité à gauche nécessite la démocratisation d’outils de “sécurité”, tels que des outils de détection de secrets, d’analyse de dépendances et de code statique etc… Certains doivent en effet être accessibles aux équipes de développement, pour les aider à vérifier la sécurité de leur code et à corriger les vulnérabilités. Ces outils doivent cependant être compréhensibles, répondre à leurs besoins et ne pas être une charge de temps supplémentaire trop importante.
Quelles sont les meilleures pratiques de sécurité Shift Left ?
Pour s’assurer de la pérennité et de la bonne mise en place de la sécurité Shift Left, plusieurs bonnes pratiques peuvent être appliquées.
Dans un premier temps, les équipes de développement doivent être formées. En effet, avec l’approche Shift Left ces équipes, portent maintenant une partie de la responsabilité de la sécurité. Elles doivent alors avoir des connaissances de bases sur des sujets de sécurité qui vont à présent les concerner, être informés des bonnes pratiques, et savoir utiliser les outils de sécurité qui leur sont confiés.
Les équipes doivent également être sensibilisées. Elles doivent apprendre à connaître les impacts d’un manque de sécurité et être informées de nouvelles menaces et risques. Pour maximiser son impact et rendre cet apprentissage plus ludique, cette sensibilisation peut prendre l’aspect d’ateliers et de jeux.
La collaboration entre les différents corps de métiers doit également être renforcée. Ceci s’applique notamment durant la phase de planification pour s’assurer que l’application sera « secure by design ».
Les bonnes pratiques et politiques de sécurité doivent être régulièrement révisées. Un point annuel permet par exemple d’être sûr qu’elles sont toujours d’actualité, et dans le cas contraire de les faire évoluer. Les personnes concernées par ces changements doivent en être informées, et la mise en pratique doit être contrôlée.
Les mesures de sécurité doivent également être automatisées. Cela permet de s’assurer de leur exécution, de réduire leur charge temporelle imposée aux équipes, et d’éviter les erreurs humaines.
Enfin, les outils doivent être intégrés. Cela peut être en local dans les IDE, mais également dans les SCM, dans les pipelines CI/CD ou encore dans les outils de ticketing.
Quels outils sont utilisés pour la sécurité Shift Left ?
Analyse de la composition logicielle (SCA, Software Composition Analysis)
Les outils de SCA analysent les composants tiers du code tels que les dépendances directes et indirectes. Ils permettent à la fois d’obtenir des informations sur les licences afin de gérer leur conformité, et d’identifier les composants ayant des vulnérabilités.
Tests statiques de sécurité des applications (SAST, Static Application Security Testing)
Les outils de SAST permettent l’identification de vulnérabilités dans le code source. Ces tests sont effectués sans exécution de l’application. Des erreurs telles que des secrets codés en dur ou des algorithmes de chiffrement trop faibles sont mises en lumière. Les résultats de ces tests procurent les emplacements précis (fichiers et lignes) des potentielles vulnérabilités.
Tests dynamiques et interactifs de sécurité des applications (DAST, Dynamic Application Security Testing, IAST, Interactive Application Security Testing)
Les DAST et IAST permettent l’analyse du comportement de l’application en fonctionnement et détectent des failles telles que le Cross-Site Scripting (XSS) ou encore les injections SQL.
Les outils DAST ne permettent pas d’identifier précisément la source des vulnérabilités dans le code contrairement aux IAST. Cependant, les IAST étant des tests hybrides entre SAST et DAST, ils doivent être adaptés au langage de programmation utilisé.
Scan d’images de conteneurs
Les images de conteneurs sont généralement composées de plusieurs couches pouvant présenter des vulnérabilités. Il est donc important de les scanner, notamment l’image de base pour vérifier qu’elle ne contient pas de vulnérabilités critiques.
Scan de fichiers de configuration IaC
Scanner les fichiers de configuration peut permettre d’identifier des vulnérabilités telles qu’une mauvaise gestion des accès aux instances et configurations réseau ou l’exposition de données sensibles.
Parmi les dizaines d’outils existants, voici notre sélection selon trois catégories.
Les outils couteaux suisses
Certains outils offrent un très large éventail de fonctionnalités. C’est notamment de cas de Snyk et Checkmarx qui sont capables d’effectuer du SCA, SAST, du scan d’images de conteneur et de fichiers d’IaC. Checkmarx est également capable de réaliser du DAST.


Les outils open-source et gratuits
L’Open Worldwide Application Security Project (OWASP) est à l’origine de plusieurs outils open-source et gratuits. Parmi eux, on retrouve Dependency-Check, un outil de SCA, et ZAP, un outil de DAST.

Les outils stars
Certains outils sont devenus des références.
C’est le cas de SonarQube, une solution d’amélioration de la qualité qui effectue de l’analyse de code statique (SAST).
Dans une autre catégorie, il existe Aqua Security qui possède notamment Trivy, un scanner permettant d’analyser les images de conteneurs et les fichiers d’IaC.


Combien peut coûter l'application de l'approche Shift Left Security ?
L’application de l’approche Shift Left peut est couteuse. Ces coûts vont dépendre des besoins de l’entreprise mais également de ses contraintes.
Les coûts proviennent du tarif lié aux offres des outils. En effet, le montant peut varier selon le nombre de lignes de code à analyser mais également le choix de l’offre (nombre d’utilisateurs, fonctionnalités, options de configuration).
En plus de ces coûts financiers, il est important d’avoir conscience de mise en œuvre. Ceux-ci sont dus à la mise en place des changements nécessaires telle que la formation des utilisateurs, mais également au temps d’analyse et de traitement des résultats.
Estimer ces coûts nécessite une expertise technique afin de trouver la solution la plus adaptée.
Comment Qim info peut vous accompagner ?
L’approche de sécurité Shift Left a donc pour objectif de mettre en place la sécurité le plus tôt possible dans le cycle de vie de développement logiciel. Elle permet de mieux limiter les vulnérabilités et est un beau premier pas vers le DevSecOps. Attention à ne pas négliger la sécurité en fin de cycle. Ne vous contentez pas d’appliquer des mesures de sécurité au début, restez vigilant car de nouvelles vulnérabilités peuvent apparaitre en cours de fonctionnement.
Pour vous aider à adopter et à appliquer l’approche Shift Left à la sécurité, notre département Cloud & DevOps Solutions vous propose plusieurs types d’accompagnement.
Des missions de conseil peuvent être réalisées si vous souhaitez en savoir plus sur la sécurité Shift Left et comment la mettre en place dans votre entreprise. Pour cela, des ateliers d’accompagnement et d’échange peuvent être organisés afin de sensibiliser aux impacts du Shift Left de la sécurité et pour trouver la solution qui vous convient le mieux. Après une phase d’analyse de votre système et de vos besoins, le département peut également mettre à profit son expertise technique pour l’implémentation et la configuration d’outils.